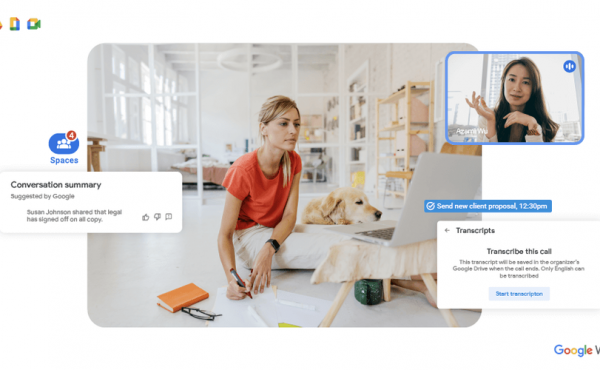
Google Workspace’s upcoming features based on Artificial Intelligence
“We didn’t get bored” – more than 20 updates to Chrome Enterprise, Google Workspace (ex. G Suite), and Google Cloud
Data security is one of our biggest challenges, and Google Cloud is taking it up. Google Cloud and Google Workspace (formerly G Suite) are constantly working to help organizations keep up with growing threats, protect their sensitive data, and enhance their security capabilities.
Therefore, in the past few weeks, Google has announced a wide range of security products and improvements. We thought putting all the news in one convenient place would be useful.
Here’s a quick summary of Google’s security announcements in the first quarter of 2018.
Chrome Enterprise
1. New partnership for enterprise mobility management (EMM)
Google has announced four new partnerships with EMM vendors to help IT administrators manage and enforce security policies across their entire fleet of devices from one location. Cisco Meraki, Citrix XenMobile, Watson’s IBM MaaS360, and ManageEngine Mobile Device Manager Plus now support Chrome Enterprise.
2. Improved Active Directory in Chrome OS
Building on Chrome OS’s integration with Active Directory last August, Google has added several improvements to help administrators manage Chrome OS and legacy infrastructure. These include the ability to authenticate at endpoints with Kerberos and NTLMv2 on local networks directly from Chrome OS, support for standard corporate Active Directory settings such as multi-domain scenarios, and support for existing certificates.
3. Advanced management options in the Chrome browser and Chrome OS
Chrome Enterprise allows administrators to set up over 200 security policies and provide employees with secure access to online resources. Google has added even more controls this month, including an extension blacklist.
Cloud Identity
4. Cloud Identity
Cloud Identity – the price of a new, autonomous solution of Identity as a Service (IDaaS), as it promotes such high-class functions in one space, as security for cloud recording, as well as for additions and management of attachments. For gloomy identification, workers get simple, secure access to their business add-ons and add-ons. Administrators get the necessary tools to manage all of them in one integration console.
Google Cloud Platform
5. Access Transparency
Trust is paramount when choosing a cloud provider, and Google wants to be as open and transparent as possible. Access Transparency gives you real-time access to logs when Google Cloud Platform administrators access your content, offering an audit trail of actions taken by your Google engineers.
6 Cloud Armor
Cloud Armor is a new distributed denial of service (DDoS) attack and application protection service based on the same technologies and global infrastructure that Google uses to protect services like Search, Gmail, and YouTube. Global HTTP(S) load balancing protects against infrastructure DDoS attacks. Cloud Armor works with HTTP(S) and allows you to customize the protection for your web applications. Its features include IP blacklisting and whitelisting, geo-based access control, custom rule assignment, and protection against attacks such as SQL Injection. Below we will show you how to set up IP blacklists and whitelists using Cloud Armor:
7. Cloud Security Command Center (alpha)
The new Cloud Security Command Center (Cloud SCC) is a data security platform that lets you view, analyze and monitor your cloud asset inventory, check sensitive data storage systems, identify common network vulnerabilities and view access rights to your resources – all from one central location. Dashboards Monitor threats and suspicious activity with Google detection and security partners such as Cloudflare, CrowdStrike, Dome9, Palo Alto Networks, Qualys, and RedLock.
8. Cloud Data Loss Prevention (DLP) API
The DLP API lets you detect, classify and modify sensitive data in real-time. And because it’s an API, you can use it on almost any data source or business application, whether in GCP services like Cloud Storage or BigQuery, third-party apps, or your local data center.
9. VPC Service Controls
Currently, VPC Service Controls helps businesses keep sensitive data private with GCP’s fully managed storage and processing. VPC Service Controls create a security perimeter around data stored in GCP services based on the Cloud Storage, BigQuery, and Bigtable APIs. This helps mitigate the risks associated with data filtering through stolen IDs, IAM policy misconfigurations, malicious insiders, and compromised virtual machines.
Google Workspace (formerly G Suite)
10. New anti-phishing features
Updated security elements can be configured to automatically update and enable Google-recommended protection. The new default protection system can:
- Automatically flag email messages from untrusted senders with encrypted attachments or embedded scripts.
- Warn if attackers are trying to spoof employees’ email addresses or if they are writing from a domain that looks like your own domain.
- Offer advanced protection against phishing attacks by pointing to an authorized email.
- Scan an image for phishing indicators and shorten URLs to detect malicious links.
11. Default mobile phone control
Core Application Management is automatically enabled for mobile devices with access to Google Workspace (ex., G Suite) accounts. Employees don’t need to set up profiles on iOS and Android devices; administrators get additional security controls, including the ability to enforce security PINs, wipe sensitive data, and see which devices access corporate data.
12. New additions to the Google Workspace Security Center (ex., G Suite)
Google introduced a new security center earlier this year for Google Workspace (ex., G Suite). The Security Center combines analytics and actionable recommendations to help you protect your organization’s data and your users’ personal data. Last week, Google introduced new additions, including:
- New security diagrams showing OAuth activity, Business Email Compromise (BEC) threats, and targeted phishing emails that may be missing the correct links.
- New mobile device management charts to help IT administrators explore activity analytics and discover when devices have been stolen or broken.
- Ability to reorganize the toolbar to focus on what matters most to your organization.
- Analyze your organization’s security posture and receive personalized advice on deploying key security features and protection against phishing attacks.
13. Security and Management for Shared Drives
New enhancements to Shared Drives provide additional security controls, including the ability to restrict file permissions and add items to prevent users from printing, downloading, and copying files. These new security features will be rolled out in the coming weeks.
Partnerships
14-25. New and expanded security partnerships
Google announced 11 new security partnerships – Auth0, Check Point, Cloudflare, Dome9, Fortinet, Palo Alto Networks, Qualys, Rackspace, RedLock, StackRox, and Sumo Logic.
- Dome9 developed the Payment Card Industry Data Security Standard (PCI DSS) compliance test suite in the Dome9 Compliance Engine.
- Rackspace Managed Security provides enterprises with additional security on top of GCP.
- The RedLock Cloud 360 Platform is a cloud threat protection solution that provides additional control for Google Cloud environments.
We believe a safer business landscape is better for everyone, so we are committed to finding new ways to help businesses be safer. Leave your request on the contact page for more information, a presentation, or a demo.